As a disclaimer, you should know that the list below is just a starting point. Use it, but do a bit more research as well. Safely decrypting your data can be a nerve-wrecking process, so try to be as thorough as possible.
We’ll do our best to keep this list up to date, but it’ll probably never be definitive. Contributions and suggestions are more than welcome, as we promise to promptly follow up on them and include them on the list.
If your computer gets infected with ransomware, here is how to recover your data:
Step 1: Do not pay the ransom because there is no guarantee that the ransomware creators will allow you to recover your data.
Step 2: Find any available backups you have.
Step 3: If there are no back-ups, you will need to try to decrypt the information locked by ransomware by using the best ransomware decryption tools available.
In this anti-ransomware guide, we included these tools below and a very useful checklist to avoid all types of malware. Use the links below to navigate through it.
How to identify the ransomware you’ve been infected with
Ransomware decryption tools
Explanation on ransomware families and tools for decryptio
How to avoid ransomware in the future
Quick checklist for ransomware protection
Ransomware decryption tools
Explanation on ransomware families and tools for decryptio
How to avoid ransomware in the future
Quick checklist for ransomware protection
How to identify the ransomware you’ve been infected with
Sometimes, the ransom note says what type of ransomware your files have been encrypted with, but it can happen that you don’t have this information at hand. Readers have asked us to show which encryption extensions belong to which ransomware families. Many of these extensions signaled new types of encrypting malware, for which there are no decryptors available.
If you need help with identifying what ransomware your system has been infected with, there are two tools you can use:
CRYPTO SHERIFF FROM NO MORE RANSOM
ID RANSOMWARE FROM MALWAREHUNTER TEAM
Please read the terms and conditions specific to these tools before using them.
Ransomware decryption tools – an ongoing list
As a disclaimer, you should know that the list below is just a starting point. Use it, but do a bit more research as well. Safely decrypting your data can be a nerve-wrecking process, so try to be as thorough as possible.
We’ll do our best to keep this list up to date, but it’ll probably never be definitive. Contributions and suggestions are more than welcome, as we promise to promptly follow up on them and include them on the list.
Some of the ransomware decryption tools mentioned below are easy to use, while others require a bit more tech knowledge to break. You can try asking for help on one of these malware removal forums, which feature tons of information and helpful communities.
Agent.iih decrypting tool (decrypted by the Rakhni Decryptor)
Aura decrypting tool (decrypted by the Rakhni Decryptor)
AutoIt decrypting tool (decrypted by the Rannoh Decryptor)
Cryakl decrypting tool (decrypted by the Rannoh Decryptor)
Crybola decrypting tool (decrypted by the Rannoh Decryptor)
Cryptokluchen decrypting tool (decrypted by the Rakhni Decryptor)
CrySIS decrypting tool (decrypted by the Rakhni Decryptor – additional details)
Democry decrypting tool (decrypted by the Rakhni Decryptor)
Fury decrypting tool (decrypted by the Rannoh Decryptor)
Lamer decrypting tool (decrypted by the Rakhni Decryptor)
Lortok decrypting tool (decrypted by the Rakhni Decryptor)
Pletor decrypting tool (decrypted by the Rakhni Decryptor)
Rotor decrypting tool (decrypted by the Rakhni Decryptor)
Explanation on ransomware families and tools for decryption
As you may have noticed, some of these ransomware decryption tools work for multiple ransomware families, while certain strains have more than one solution (although this is rarely the case).
From a practical perspective, some of the decryptors are easy to use, but some require some technical know-how. As much as we’d want this process to be easier, it doesn’t always happen.
No matter how much work and time researchers put into reverse engineering cryptoware, the truth is that we’ll never have a solution to all of these infections. It would take an army of cyber security specialists working around the clock to get something like this done.
How to avoid ransomware in the future
Being pragmatic doesn’t mean adopting a pessimistic outlook. In fact, if you apply the simple steps we outlined in the anti-ransomware security plan, you can avoid this kind of attacks and the need to use ransomware decryption tools to recover your data.
Even if cyber criminals do manage to infect your PC, you can just wipe the system clean and restore your latest backup. No money lost and, most importantly, no important information compromised! So, please, please back up your data. Not tomorrow, not this weekend, not next week. Do it today!
I hope that it will solve some of your ransomware-related problems. Moreover, please think about sharing the simple principle of proactive protection with your friends and family. It could spare them the negative experience of being a cyber attack victim.
As new types of ransomware emerge, researchers decrypt some strains and others get new variants. There are tens or hundreds of them. Just like in a cat and mouse game, the chase never stops.
If this graphic would be filled out with the discoveries until 2018, you’d need a bigger screen (possibly 3) to see this.
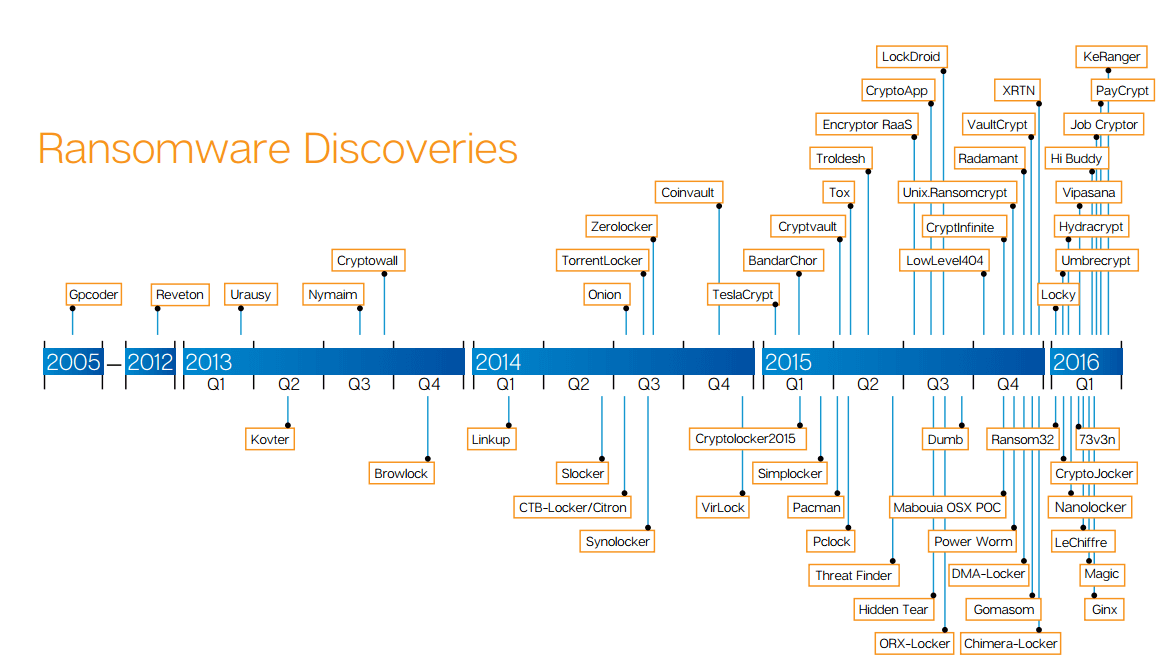
Source: CERT-RO
Believe it or not, there is a silver lining to ransomware’s popularity: the quality of the malicious code is steadily decreasing. As a result, cyber security specialists can crack the code faster. This gives ransomware victims a change to retrieve their data without further funding attackers.
Unfortunately, low quality ransomware also endangers the affected data: one error in the code and it can all be erased instead of encrypted. But that’s a story for another time.


Hi,
ReplyDeleteThanks for sharing your blog. It was very nice. Fast Data Recovery is one of the most recommended dharma ransomware recovery service provider with 24*7 support with guarantee to recover from all types of virus. We have a dedicated team working around the clock in decrypting, analyzing and preventing your data. For more information feel free to contact us anytime.
Selling USA FRESH SSN Leads/Fullz, along with Driving License/ID Number with good connectivity.
ReplyDelete**Price for One SSN lead 2$**
All SSN's are Tested & Verified. Fresh spammed data.
**DETAILS IN LEADS/FULLZ**
->FULL NAME
->SSN
->DATE OF BIRTH
->DRIVING LICENSE NUMBER
->ADDRESS WITH ZIP
->PHONE NUMBER, EMAIL
->EMPLOYEE DETAILS
->Bulk order negotiable
->Hope for the long term business
->You can asked for specific states too
**Contact 24/7**
Whatsapp > +923172721122
Email > leads.sellers1212@gmail.com
Telegram > @leadsupplier
ICQ > 752822040